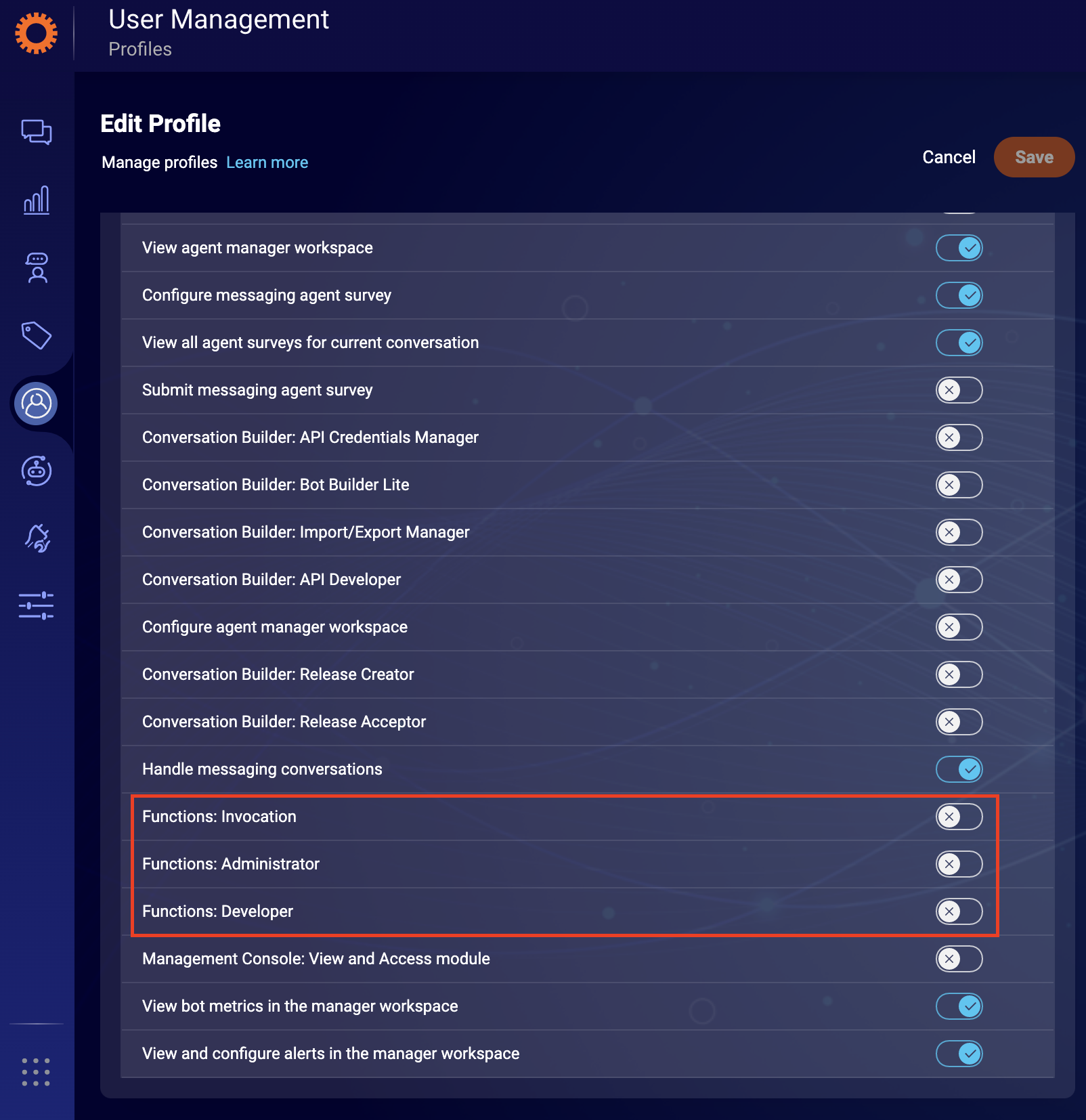
There are three user permissions concerning Functions:
- FaaS-Admin: allowed to read
lambdas, manage the allowlist for external domains and manage secrets. By default, this permission is set to 'ON' for all admins on the account. It is, however, possible to limit your admin's access as well. You may create a separate permission group for developers you wish to have part of the admin profile permissions and assign them with the necessary permissions by creating a custom profile. - FaaS-Developer: allowed to manage
lambdas, read allowlisted domains and read encrypted secrets. - FaaS-Invocation: provides read access to all functions and permission to invoke them. The Agent profile has this permission enabled by default.
Permissions by role
Only the Administrator role has all the Function permissions enabled by default as described below.
Agent Manager roles will have all Function permission disabled by default, and Agents only will be able to have FaaS-Invocation permissions.
| Permission name | Agent | Agent Manager | Campaign Manager | Admin |
|---|---|---|---|---|
| FaaS-Admin | ❌ | 🔒 | ❌ | ✅ |
| FaaS-Developer | ❌ | 🔒 | ❌ | ✅ |
| FaaS-Invocation | 🔒 | 🔒 | ❌ | ✅ |
If users who do not have an Administrator based role require any Functions-related permissions below, please manage the user profile permission from the User Management tab in your LivePerson account.
Table Legend
- ❌: Permission is Not available for the role.
- 🔒: Permission is disabled by default but can be enabled.
- ✅: Permission is available and enabled.
Permissions details
| Component | Action | FaaS-Admin | FaaS-Developer | FaaS-Invocation |
|---|---|---|---|---|
| lambda | read | ✅ | ✅ | ✅ |
| lambda | create/edit/delete | - | ✅ | - |
| lambda | deploy | - | ✅ | - |
| lambda | invoke | - | ✅ | ✅ |
| whitelist | create/edit/delete | ✅ | - | - |
| whitelist | read | ✅ | ✅ | - |
| secret | create/edit/delete | ✅ | - | - |
| secret | read (value is obfuscated) | ✅ | ✅ | - |
| schedule | read | ✅ | ✅ | ✅ |
| schedule | create/edit/delete | ✅ | ✅ | - |
| emailReport settings | create/edit/delete | ✅ | - | - |
| emailReport recipients | create/delete | ✅ | ✅ | - |
| emailReport | read | ✅ | ✅ | ✅ |
| logs | read | ✅ | ✅ | ✅ |
| logs | create | ✅ | - | - |
| reporting | read | ✅ | ✅ | ✅ |
Please be aware only a FaaS Developer or FaaS Admin may access the FaaS UI, the FaaS Invoker can not access the FaaS UI.
You may configure these permissions in Conversational Cloud. More info on adding permissions can be found here. The process is simple:
- Select Users tab at the top of the Conversational Cloud UI and then click profiles.
- Create/Edit a profile and add the relevant FaaS-* permission to it.
Hints
- Please be aware that roles like Agent do not have the option to get FaaS Developer/Admin permission. You will need to use a different role in that case.
- The CLI leverages the same permissions. Therefore you need to ensure that the user used has at least the FaaS-Developer permission.
- We suggest obeying the security principle of least privilege and, therefore, only selecting the minimal set of permissions, e.g. if the user will only invoke functions solely, the FaaS-Invocation is required.